Modern software delivery moves fast, but speed without security creates compounding risk. As organizations adopt CI/CD pipelines, containerization, and cloud-native architectures, vulnerabilities can be introduced into codebases faster than security teams can manually review them. DevSecOps shifts security left, embedding automated scanning into development workflows so vulnerabilities are detected and fixed before reaching production. Choosing the right security scanning tools is critical to making that vision practical and scalable.
TLDR: Integrating security scanning tools directly into CI/CD pipelines allows teams to detect vulnerabilities early, reduce remediation costs, and prevent production incidents. Leading DevSecOps tools cover source code, open-source dependencies, containers, and infrastructure as code. This article reviews four trusted solutions—Snyk, Checkmarx, Aqua Security, and GitLab Security—highlighting their strengths and ideal use cases. A comparison chart at the end helps teams evaluate which tool best fits their environment.
Security scanning in DevSecOps environments generally falls into four categories:
- Static Application Security Testing (SAST) – analyzes source code for flaws.
- Software Composition Analysis (SCA) – identifies vulnerabilities in third-party dependencies.
- Container and Kubernetes scanning – detects misconfigurations and vulnerable images.
- Infrastructure as Code (IaC) security – validates Terraform, CloudFormation, and similar configurations.
Below are four security scanning tools that stand out for their early detection capabilities, seamless CI/CD integration, and enterprise readiness.
1. Snyk
Snyk has become one of the most recognized names in developer-first security. Its strength lies in making vulnerability detection accessible directly within developer workflows, including IDEs, pull requests, and CI pipelines.

Core Capabilities:
- Software Composition Analysis (SCA): Identifies known vulnerabilities in open-source libraries.
- Container scanning: Detects vulnerabilities in Docker images and base layers.
- Infrastructure as Code scanning: Flags misconfigurations in Terraform, Kubernetes manifests, and AWS CloudFormation.
- Code scanning: Provides SAST functionality for identifying application flaws.
One of Snyk’s most valuable features is its developer-centric remediation advice. Instead of simply flagging vulnerabilities, it provides prioritized fix recommendations and automated pull requests to upgrade dependencies.
Why it detects vulnerabilities early:
- Integrates natively with GitHub, GitLab, and Bitbucket.
- Runs automatically during pull requests.
- Offers CLI tools for embedding into CI workflows.
For organizations focused heavily on open-source software and cloud-native development, Snyk provides comprehensive coverage with minimal friction. However, in large enterprise environments requiring deep code analysis customization, other specialized SAST tools may offer more granular control.
2. Checkmarx
Checkmarx is an enterprise-grade application security testing platform known for its robust Static Application Security Testing engine. It is particularly well-suited to organizations with complex codebases and strict compliance requirements.
Core Capabilities:
- Advanced SAST: Deep code analysis across multiple programming languages.
- Interactive Application Security Testing (IAST): Runtime analysis during automated testing.
- Software Composition Analysis: Open-source dependency checks.
- Policy management: Customizable security rules and governance controls.
Unlike lighter-weight developer tools, Checkmarx focuses on highly accurate analysis with reduced false positives when properly tuned. Security teams gain detailed reporting, audit trails, and compliance alignment for standards such as OWASP Top 10 and PCI-DSS.
How it integrates into CI/CD:
- Plugins for Jenkins, Azure DevOps, GitHub Actions, and more.
- Automated scans triggered on code commits.
- API-based integration with security orchestration platforms.
Because it performs deep analysis, scan times may be longer compared to lighter tools. However, for organizations where accuracy and auditability are priorities, Checkmarx provides a strong security foundation.
3. Aqua Security (Trivy)
As container adoption accelerates, image scanning has become non-negotiable. Aqua Security provides a platform specifically built for containerized and cloud-native environments. Its open-source tool, Trivy, is widely used for early vulnerability detection.

Core Capabilities:
- Container image scanning: Identifies OS package and application vulnerabilities.
- Kubernetes configuration checks: Flags insecure workload definitions.
- Infrastructure as Code scanning: Evaluates Terraform and cloud templates.
- Runtime protection (enterprise version): Detects threats during execution.
Trivy’s simplicity is one of its major strengths. It can scan images, repositories, or file systems with a single command, making it easy to embed directly into build pipelines.
Benefits for CI/CD environments:
- Lightweight CLI tool ideal for automated builds.
- Fast scanning designed for ephemeral containers.
- Supports shift-left scanning before images are pushed to registries.
Aqua’s enterprise platform adds policy enforcement, compliance reporting, and runtime visibility, making it suitable for regulated sectors running Kubernetes at scale.
4. GitLab Security (Built-in DevSecOps)
GitLab offers an integrated DevSecOps platform that embeds security testing directly into the CI/CD pipeline without requiring extensive third-party tooling. This unified approach reduces integration complexity.
Core Capabilities:
- SAST and DAST: Static and dynamic testing within pipelines.
- Dependency scanning: Detection of vulnerable libraries.
- Container scanning: Image and registry security checks.
- Secret detection: Identifies exposed credentials in repositories.
Because GitLab security features are integrated natively, organizations avoid the complexity of stitching together multiple point solutions. Security dashboards consolidate findings into a single interface, improving visibility for both developers and security teams.
Why it works well for early detection:
- Preconfigured CI/CD templates for quick enablement.
- Automatic merge request security reports.
- Centralized vulnerability management.
For teams already committed to GitLab as their DevOps platform, built-in security scanning is often the most frictionless path to DevSecOps maturity.
Comparison Chart
| Tool | Primary Strength | Best For | CI/CD Integration | Enterprise Features |
|---|---|---|---|---|
| Snyk | Developer focused SCA and container scanning | Cloud native teams using open source heavily | Strong Git integrations and CLI support | Policy management and reporting |
| Checkmarx | Deep static code analysis | Large enterprises with compliance needs | Broad CI plugin ecosystem | Advanced governance and audit controls |
| Aqua Security | Container and Kubernetes security | Container heavy environments | Lightweight CLI and registry integration | Runtime protection and compliance modules |
| GitLab Security | All in one DevSecOps integration | Teams using GitLab CI pipelines | Native pipeline security stages | Unified security dashboards |
Choosing the Right Tool for Your Pipeline
No single security scanning solution fits every environment. The right choice depends on:
- Technology stack: Languages, frameworks, and infrastructure model.
- Deployment architecture: Monolith, microservices, or container-native.
- Compliance requirements: Industry regulations and audit expectations.
- Developer workflow: IDEs, repositories, and CI platforms in use.
Organizations often combine tools—for example, pairing Snyk for dependency management with Aqua for container scanning. The goal is not tool consolidation at all costs, but continuous vulnerability visibility from commit to production.
Final Thoughts
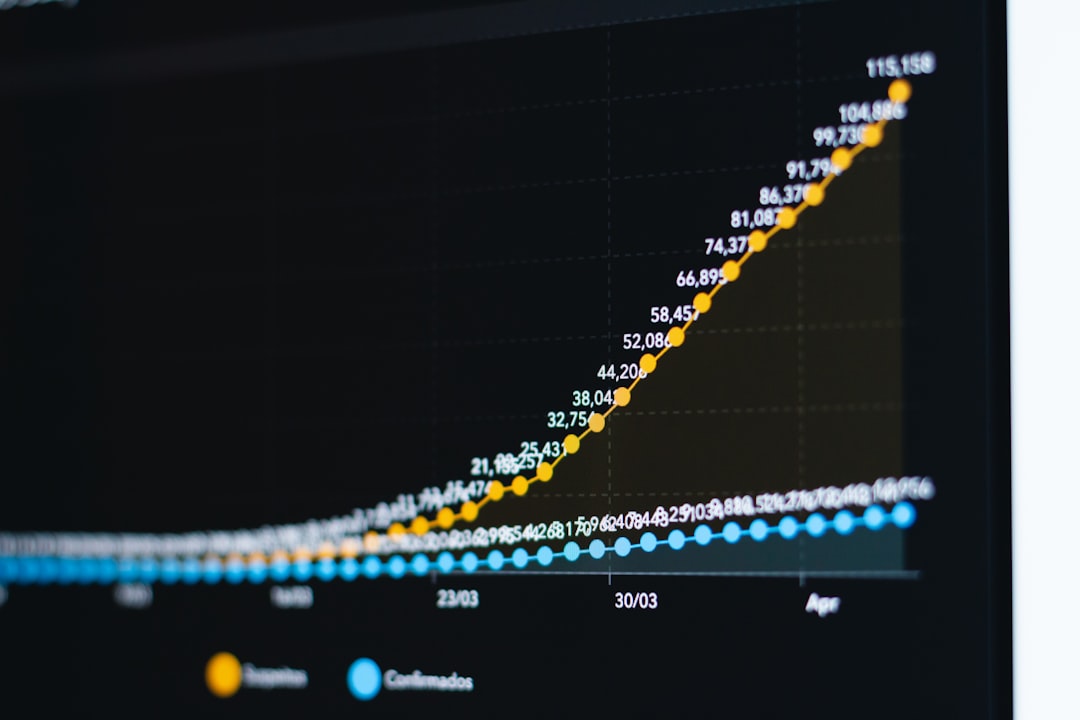
Security vulnerabilities are significantly cheaper to fix during development than after release. Industry studies consistently show remediation costs increasing exponentially the later flaws are discovered. Embedding automated scanning into CI/CD pipelines transforms security from a bottleneck into an enabler.
The four tools outlined—Snyk, Checkmarx, Aqua Security, and GitLab Security—each provide strong early detection mechanisms. Whether you prioritize developer experience, enterprise-grade code analysis, container security, or platform consolidation, these solutions demonstrate how DevSecOps can be implemented in practical, measurable ways.
Ultimately, successful DevSecOps is not just about tools. It requires cultural alignment, automation discipline, and executive support. But with the right scanning solutions integrated early into CI/CD, organizations can dramatically reduce exposure, strengthen software integrity, and move fast without compromising security.