The dark web is often described in dramatic terms, but it is simply a part of the internet that is not indexed by ordinary search engines and usually requires special software to access. It can host privacy-focused communities, whistleblowing platforms, academic resources, and secure communication tools, but it also contains scams, malware, illegal marketplaces, and disturbing content. A cautious visitor treats it as a high-risk environment, not as a place for casual browsing.
TLDR: The safest way to access the dark web is to use the official Tor Browser, keep devices updated, protect personal identity, and avoid downloading files or interacting with strangers. A responsible user should only visit known, legitimate onion sites and should leave immediately if illegal content appears. The dark web is not inherently illegal, but careless behavior can expose a person to scams, malware, surveillance, or legal trouble.
What the Dark Web Is—and Is Not
The internet is often divided into three loose categories: the surface web, the deep web, and the dark web. The surface web includes public pages found through search engines. The deep web includes pages that are not indexed, such as online banking portals, private databases, email inboxes, and subscription services. The dark web is a smaller section of the deep web that requires specialized tools, most commonly Tor, to access.
Tor, short for The Onion Router, routes traffic through multiple volunteer-operated servers, making it harder to connect a visitor’s identity with the websites being visited. This privacy design can help journalists, activists, researchers, and ordinary people communicate more safely. However, the same anonymity can attract criminals, fraudsters, and malware operators. For that reason, safe access begins with realistic expectations.

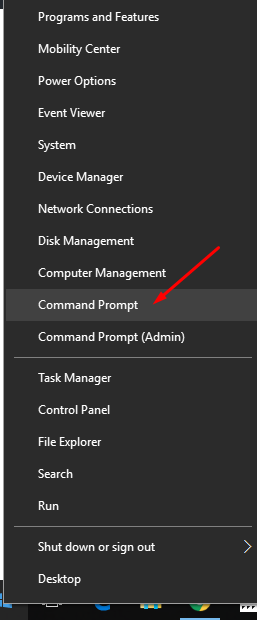
Use the Official Tor Browser
The most important safety step is to use the official Tor Browser, downloaded only from the Tor Project’s legitimate website. A person should avoid random “Tor download” links, unofficial bundles, cracked apps, or browser extensions that claim to provide dark web access. Fake versions of privacy tools are a common way attackers infect devices.
Before using Tor, the device’s operating system and security software should be updated. Updates fix known vulnerabilities that could otherwise be used to identify or compromise the user. The browser itself should also remain updated, because older versions may contain weaknesses that attackers on malicious sites can exploit.
Tor Browser is designed with privacy in mind, so users should avoid changing advanced settings unless they understand the consequences. Installing extra extensions, plugins, or themes can weaken anonymity by making the browser easier to fingerprint. In general, the safest configuration is the default one, with the security level increased when visiting unfamiliar sites.
Consider the Role of a VPN Carefully
Many guides claim that a VPN is always required for dark web access, but the reality is more nuanced. A VPN can hide Tor usage from an internet service provider, and it may add a layer of network privacy. However, it also shifts trust to the VPN company, which may log activity or respond to legal requests.
A cautious person should not assume that a VPN makes unsafe behavior safe. It does not protect against scams, malicious downloads, phishing, or voluntary disclosure of personal information. If a VPN is used, it should be a reputable paid service with clear privacy policies, strong security practices, and no unrealistic promises. Free VPNs are often risky because some collect data, inject ads, or provide weak protection.
Separate Dark Web Activity From Personal Identity
Privacy depends heavily on behavior. Even when Tor works correctly, a person can defeat anonymity by logging into personal accounts, reusing usernames, mentioning identifying details, or opening documents that connect back to a real identity. Safe access means keeping dark web activity separate from everyday digital life.
- Do not log into personal email, banking, social media, or work accounts through Tor.
- Do not reuse usernames, profile photos, passwords, or writing styles associated with real-world identity.
- Do not share personal details such as location, employer, school, phone number, or birth date.
- Do not use regular payment methods or provide financial information on onion sites.
- Do not mix research activity with personal browsing in the same session.
Some users choose to access Tor from a separate device or a privacy-focused operating system. This can reduce risk, but it is not a substitute for careful habits. Most privacy failures happen because someone reveals too much, clicks the wrong thing, or trusts the wrong person.
Visit Only Known and Legitimate Onion Sites
Dark web addresses are often long and difficult to remember. Search engines and link directories may include outdated, fake, or malicious links. A visitor should rely on trusted sources, official websites, or well-known organizations that publish their onion addresses on their regular public websites.
Examples of legitimate uses can include secure news submission portals, privacy-focused email services, nonprofit resources, and censorship-resistant information sites. Even then, onion addresses should be checked carefully. Phishing is common, and attackers often create lookalike sites designed to steal credentials, cryptocurrency, or sensitive information.

Avoid Downloads, Scripts, and Unknown Files
Downloading files from the dark web is one of the fastest ways to create risk. Files can contain malware, tracking beacons, exploit code, or hidden metadata. Documents such as PDFs, Word files, and images may reveal information when opened outside Tor Browser or in ordinary applications connected to the internet.
If a file must be handled for legitimate research, it should be treated as potentially hostile. A careful researcher uses an isolated environment, keeps software patched, and avoids opening files on a primary personal or work device. For most people, the safest rule is simple: do not download anything from unknown dark web sources.
Scripts are another danger. Tor Browser includes security settings that can restrict JavaScript and other active content. Increasing the security level can break some sites, but it also reduces exposure to browser-based attacks. A person who values safety should prefer broken pages over unnecessary risk.
Know What to Avoid
The dark web contains content and services that can be illegal, harmful, or fraudulent. A responsible user should avoid areas involving stolen data, weapons, drugs, counterfeit documents, hacking services, exploitation, extremist activity, or any form of abuse. Merely entering such spaces can create legal, ethical, and security risks.
Scams are extremely common. Many “marketplaces” are designed to steal money, credentials, or cryptocurrency. Some sites pretend to sell illegal goods but are operated by criminals, scammers, or law enforcement. Others use fake reviews, escrow tricks, and impersonation to create false confidence. The safest approach is not to engage at all.
If illegal or disturbing content appears unexpectedly, the user should close the page immediately. They should not save, share, screenshot, or interact with the material. If the content involves immediate harm or abuse, reporting options may exist through appropriate national or local authorities.
Protect Accounts, Passwords, and Devices
Dark web browsing should be paired with strong general security. Password managers help create unique passwords for legitimate services, reducing the damage if one account is compromised. Multi-factor authentication protects accounts even if a password leaks. Device encryption helps protect stored data if a laptop or phone is lost.
A person should also watch for signs of compromise: unexpected pop-ups, new browser behavior, unknown apps, disabled security tools, or unusual account login alerts. If something suspicious happens after dark web activity, the safest response is to disconnect from the network, run reputable security scans, change important passwords from a clean device, and seek expert help if needed.
Understand Legal and Workplace Risks
Accessing Tor is legal in many countries, but laws vary. Some governments restrict anonymity tools or watch their use closely. A person should understand local rules before accessing the dark web. In workplaces, schools, or public institutions, using Tor may violate acceptable-use policies even if the activity itself is lawful.
Legal risk also depends on conduct. Viewing privacy resources is very different from seeking stolen information, buying prohibited items, or joining criminal forums. A safety-minded user avoids anything that could support crime or harm others. Curiosity is not a defense against reckless behavior.

Best Practices for Safer Dark Web Access
- Use only the official Tor Browser and keep it updated.
- Update the operating system before browsing.
- Increase Tor Browser’s security level when visiting unfamiliar pages.
- Use trusted onion addresses from official sources.
- Avoid downloads, unknown links, and file attachments.
- Never provide personal, financial, or identifying information.
- Do not engage with illegal markets or services.
- Close suspicious pages immediately and clear the session when finished.
- Keep dark web activity separate from personal accounts and normal browsing.
- Remember that anonymity is a practice, not a guarantee.
Final Thoughts
The dark web is best approached with caution, restraint, and a clear purpose. It can provide meaningful privacy benefits for people who need secure access to information or communication, but it is not a playground. The safest visitor uses verified tools, avoids risky interactions, refuses illegal content, and protects identity at every step.
Ultimately, safe access depends less on secret technology and more on disciplined behavior. A person who does not download unknown files, does not trust strangers, does not reveal personal details, and does not engage in illegal activity greatly reduces the most common risks. The dark web may be hidden from ordinary search engines, but its dangers are very real.
FAQ
Is it illegal to access the dark web?
In many places, accessing the dark web through Tor is not illegal by itself. However, laws vary by country, and illegal activity remains illegal regardless of the browser being used.
Is Tor the same as the dark web?
No. Tor is a privacy network and browser. The dark web refers to sites and services that require special tools, such as Tor, to access.
Does a VPN make dark web browsing completely safe?
No. A VPN may hide Tor usage from an internet service provider, but it does not stop phishing, malware, scams, or careless identity disclosure.
Can someone be tracked on the dark web?
Yes. Tor improves privacy, but tracking can still happen through malware, browser fingerprinting, account logins, personal mistakes, malicious downloads, or operational security failures.
Should files be downloaded from dark web sites?
Generally, no. Unknown files may contain malware, trackers, or hidden metadata. Most users should avoid downloading anything from untrusted onion sites.
What should a person do if illegal content appears?
The page should be closed immediately. The person should not interact with, save, or share the content. If appropriate, the matter can be reported to relevant authorities.
Are dark web marketplaces safe if they have good reviews?
No. Reviews can be fake, marketplaces can be scams, and many such sites involve illegal activity. A responsible user should avoid them entirely.
What is the safest reason to use the dark web?
Legitimate uses include privacy-focused research, secure communication, accessing censored information, and using verified onion services from reputable organizations.